In previous blog posts, I’ve briefly mentioned using Pyxsoft Anti Malware for actively monitoring my server for attackers. In essence, it’s a security plugin for Web Hosting Manager for servers that run CentOS or CloudLinux. Features include blocking potential malicious uploads (authorized – such as from a form; or via an exploit) and brute force protection (like repeated WordPress login attempts). The plugin also can scan your server for malware automatically or upon request. The Pyxsoft team claims that their database has over 4 million virus definitions!
Having used Pyxsoft Anti Malware for the better part of 3 years for a charge of $5/monthly, I can confidently say that I am very pleased with the service. The plugin interface is user-friendly and easy to comprehend. There doesn’t seem to be much in the way of reviews for this plugin, but the feedback that is out there isn’t all that positive.
It seems like a major point of contention is the lack of response from the team regarding issues. The few times I’ve needed to contact the team did show some inconsistencies in response times. However, the last time was well over a year ago. I consider myself a pretty savvy troubleshooter and was able to resolve my own problems in the past. Thankfully, those were few and far between.
Pyxsoft Anti Malware in Action
HTTP Upload Inspector
The screenshot below shows a snippet of activity in regards to HTTP uploads. Date, IP Address, File Name, Upload Path, and Result detail each occurrence of an upload. As you can see, the red (malicious attempts) are frequent with PHP scripts or the revslider.zip exploit being the most popular hacking attempts. Mind you, the Revolution Slider exploit was patched several years ago, yet these idiots keep trying.
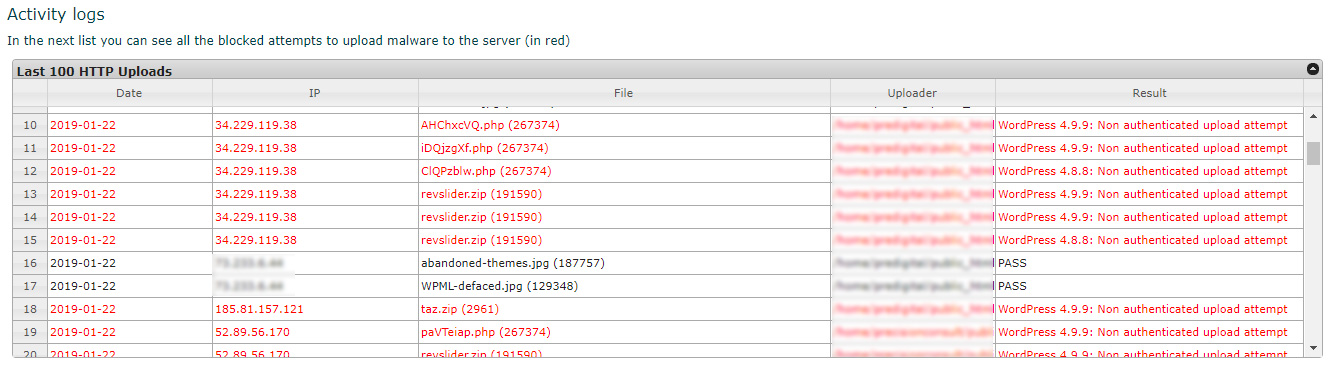
The two black colored lines are uploads by me, the red are exploit attempts.
Instant Protection
An equally important component for Pyxsoft Anti Malware is the Instant Protection feature. As the name states, attempts at manipulating core files to inject a payload are thwarted immediately. The date, IP address, target path (including domain) as well as a description of the attack are clearly defined.
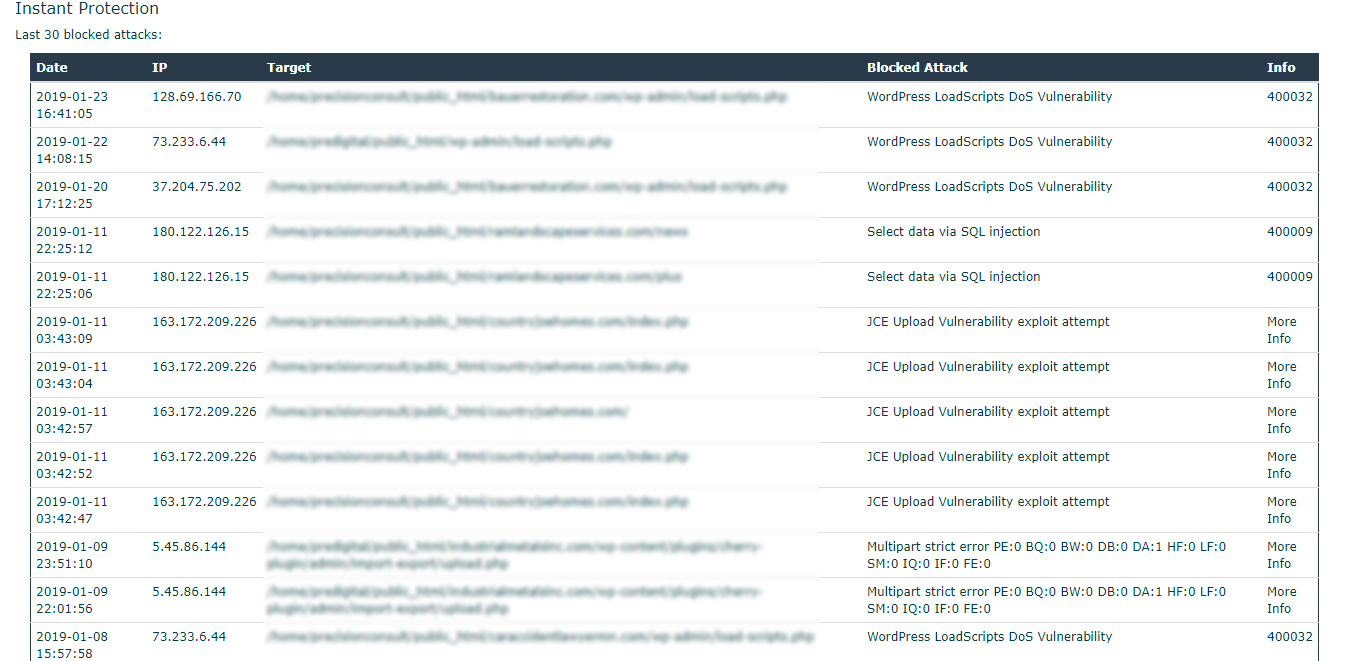
All kinds of different exploits were attempted and blocked.
Looking at the screenshot above, notice the bunch of JCE Upload Vulnerability exploit attempts? That is referring to a Joomla exploit. I’ve never even built a website with that CMS! Some of these “hackers” are clearly grasping at straws and should really go back to school. On the other hand, it seems some people are happy with trying to crash my server with Denial of Service attacks that were blocked.
Brute Force Protection
The last component I’d like to touch on is the Brute Force Protection. What this does is automatically block attackers who repeatedly guess incorrect login credentials. This is typically associated with the WordPress login page of a website, but I assume it could apply to any login page.
All of the entries shown below are for one particular domain. It’s an issue I could fix by employing the login rename feature of My Favorite Security Plugin for WordPress. This feature allows you to change the standard wp-login.php to another alias of your choosing.
The only reason I left this one particular domain with the standard login page is for testing purposes. According to the logs, it looks like Pyxsoft Anti Malware is doing its job banning people. These might even be bots using a script to guess username and password combinations.
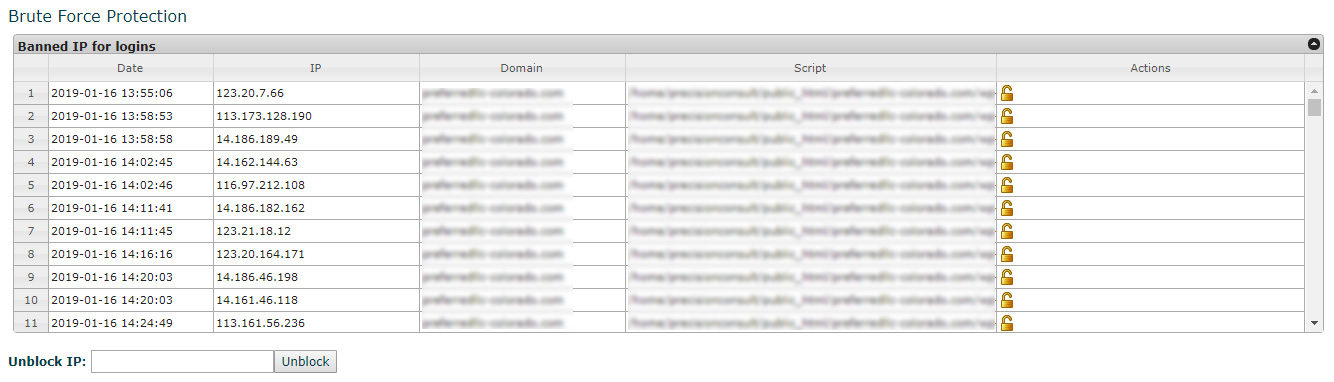
An unlock icon lets you ublock IP addresses on the fly if you wish.
What’s New in Version 2.0
I received the following email recently from the Pyxsoft team detailing all of the major changes in this new release:
Hello Ryan,
We are pleased to announce the Pyxsoft 2.0 release.
The most important features are:
- No cPanel dependencies. It means that the cPanel upgrades will not affect Pyxsoft any more.
- ClamAv was replaced by our own scanner: pxscand. ClamAV could be uninstalled from the server.
- More control over server resources: With pxscand you can control the CPU usage to avoid increments in the server load.
- Malicious symbolic links detection
- Pxscand prevents evasion techniques in malware
- Standalone product. Not a cPanel plugin any more. Anyway a link to Pyxsoft is included in WHM for you
- Instant scan engine: Files are scanned when they are created.
- HTTP inspector is now integrated as a mod security vendor in cPanel
- Compatibility with cPanel in CentOS & CloudLinux and Virtualmin in CentOS. More panels & OS coming soon
I certainly appreciate the team’s push to make the plugin independent of cPanel requirements. It’s a bit surprising to see that the popular ClamAv scanner is no longer being used either. I’ll be curious to see how much flexibility is given in regards to scanning my server. With so many accounts, it can take hours for a complete scan to finish.
According to the release notes, I should be able to give priority to either limiting precious server resources for scanning or speeding up the process. I don’t mind the length of a scan as it is done in the background. What’s important to me is having a lesser impact on the server and my client’s websites.
Try Pyxsoft Anti Malware for Free
If it weren’t for the free trial, I would have never discovered this great server plugin. I can’t remember the exact duration (perhaps a couple weeks?) but it was enough to get a feel for how it functions. There are no limitations, and when the trial expires, you simply need to purchase and enter a registration key.
For $5 a month for my VPS, I think it is totally worth it. I think the Dedicated Server key costs around $10 a month. The only other suitable alternative I’ve come across is ConfigServer eXploit Scanner (cxs). Having used their Firewall plugin, I have no doubt that it is a top-notch product. The $60 price tag seems reasonable and reviews have been favorable.
The one concern some people mentioned with cxs is the resources that it can consume as your server grows. This looks like something that the Pyxsoft team is addressing with the latest version of Anti Malware. Also, comparing the interface of Anti Malware to cxs, I’d wager that the former is a lot easier to navigate and understand for admin novices.


