News Courtesy of ZDNet.com:
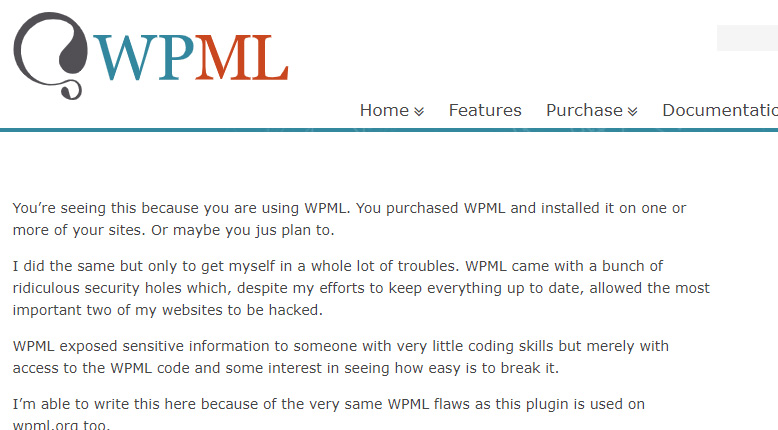
A very popular WordPress plugin was hacked over the weekend after a hacker defaced its website and sent a mass message to all its customers revealing the existence of supposed unpatched security holes. In a follow-up mass email, the plugin’s developers blamed the hack on a former employee, who also defaced their website.
The plugin in question is WPML (or WP MultiLingual), the most popular WordPress plugin for translating and serving WordPress sites in multiple languages.
According to its website, WPML has over 600,000 paying customers and is one of the very few WordPress plugins that is so reputable that it doesn’t need to advertise itself with a free version on the official WordPress.org plugins repository.
Just to be clear, the plugin itself wasn’t hacked. Rather this alleged bitter ex-employee left a backdoor to gain access to his former company’s website. While WPML was quick to notify their customers of the breach, the damage had already been done. Forced to rebuild the server, data that has been lost or comprised due to the hack has caused the company great frustration in time and money spent.
If indeed this attack was carried out by a former employee, it has to be one of the dumbest of all time. Jail time and fines are certain to follow for the perpetrator. I’m sure many of us have been unfairly treated by a former boss or two. However, that doesn’t excuse such behavior as to destroy property and harass or intimidate that company’s clients.
Reviewing the list of known vulnerabilities, it seems like all but one occurred in 2015. Reading from the notes, after being made aware of these vulnerabilities, WPML was quick to issue patches. The email/post created by the attacker claims to be a victim of the plugin’s vulnerability, however, no further information on the matter was given. Without any data to back up this claim, the “victim’s” story starts to fall apart.
Hopefully, this becomes a cautionary tale to companies that they need to really limit server access to trusted and essential employees. Personally, I’m hesitant giving any sort of privileges to my VPS to other administrators. If that becomes a problem, I’ll advise that they take their website and host it elsewhere. There is just too much at stake to even leave the possibility of an attack or hack.